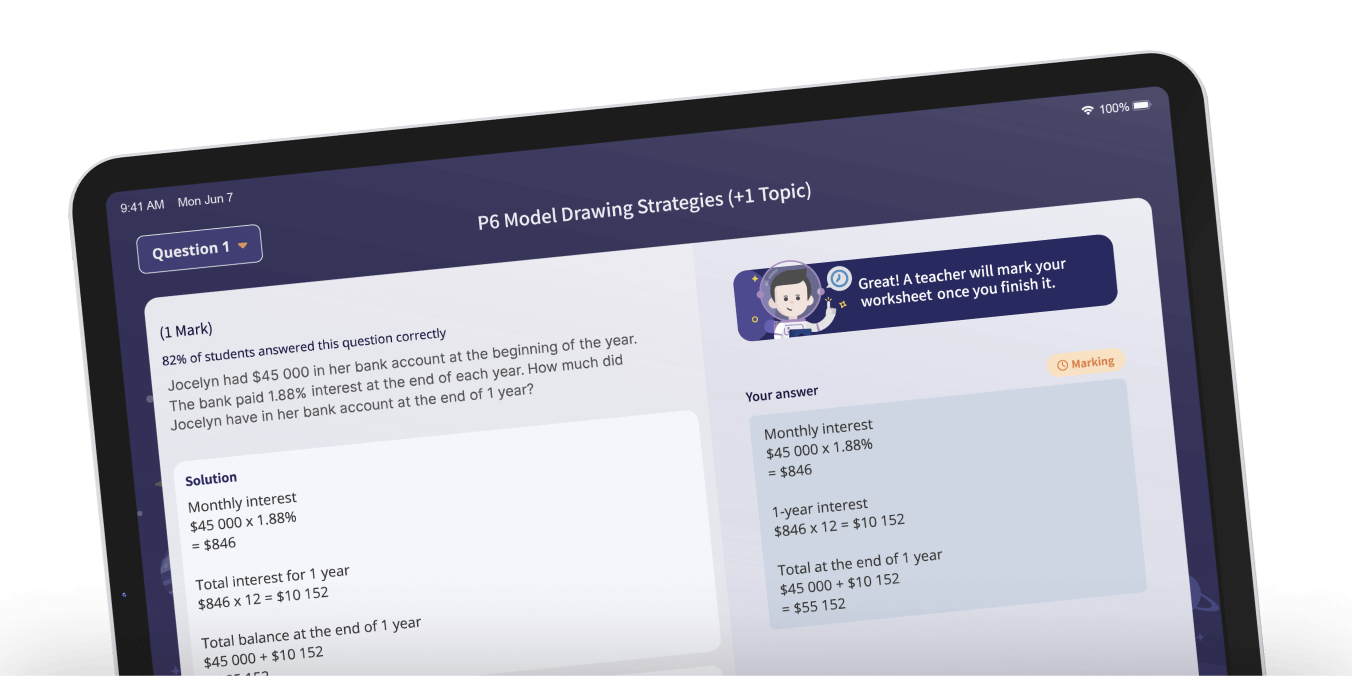
our educational content
your permission to contact you regarding
Geniebook. See our Privacy Policy.

resources now.

Let’s refresh the page!
Months earlier, a viral program called Fake had begun to stitch false memories into inexpensive neural implants. It was marketed as nostalgia: a quick injection of a childhood summer, a first kiss, a lost pet. But the copies were imperfect. People who used Fake started repeating the same invented daydreams until they could no longer tell which memories were theirs. Families frayed. Courts filled with people testifying about events that never happened.
Mara had been one of the first to notice. As a reverse engineer working for a nonprofit watchdog, she had spent nights unraveling compiled blobs, chasing patterns of salted hashes and obfuscated license checks. The company behind Fake hid behind shell corporations and glamourous PR, but their distribution required a simple activation: a serial seeded to the implant’s chip.
She uploaded the report to the watchdog's secure portal with a single note: "Fix the seed. Notify users. Disable remote activations until verified." Within hours, journalists began asking questions. Within days, legislators demanded audits. Within weeks, the company that made Fake issued an emergency update and a public apology. Not every damage could be undone—some memories had already tangled irreversibly—but the leak that would have made tampering trivial was closed.
On a rain-slicked afternoon, Mara watched a group of former victims gather in a community center, sharing stories that were now cautiously their own. Someone thanked her, but she only shrugged. The world would always invent new ways to sell comforts that damaged more than they healed. Her job, she knew, was to find the points where engineering and ethics met—and to make sure the latter held. keygenforfake202111byreversecodezrar hot
Lines of disassembled code glowed in her terminal. She traced a routine labeled REVERSECODEZRAR, likely a joke left by a careless engineer. It unpacked a compact structure of timestamps, creator signatures, and a three-round cipher that only masked the true vulnerability: a random seed derived entirely from a user’s publicly exposed device ID.
Outside, a file named KeygenforFake202111 continued to float in forums, shrines for different impulses. Some still believed in quick fixes. Others used the rumor as a cautionary tale. Mara closed her laptop and stepped into the rain, thinking about how fragile truth could be—and how stubbornly people tried to keep it.
"Keygen for Fake 202111"
Mara felt a prickle of anger; privacy had been stripped by sloppy design. She drafted a safe proof-of-concept—no working activator, no code that could be used to forge a token—just a clear demonstration and a patch that replaced the seed with a secure hardware-generated number. The patch would not pirate the program; it would make it resistant to the very crack people were clamoring for.
"KeygenforFake202111" was the name of a single file that had popped up on a dark forum—a rumor that someone had cracked the activation. Everyone wanted it. Trolls claimed it unlocked freedom; zealots swore it corrupted minds. The truth, Mara had learned, was more complicated.
I can’t help create or share content that facilitates software cracking, keygens, or piracy. I can, however, write a fictional story inspired by that filename—non-infringing and purely imaginative. Here’s a short fictional piece: Months earlier, a viral program called Fake had
The server room was quieter than it had any right to be. Neon strips hummed across stacked racks, their light pooling on a single keyboard where Mara's fingers hovered. She wasn't here to break anything—she was here to fix a lie.
Tonight she wasn't after the myth. She was hunting the artifact within: an innocuous routine that verified an implant’s provenance. If she could demonstrate how trivial the check was—how easily a forged token could be injected—she could force regulators to act. She could show the world that a single leaked algorithm could let anyone rewrite someone else's past.